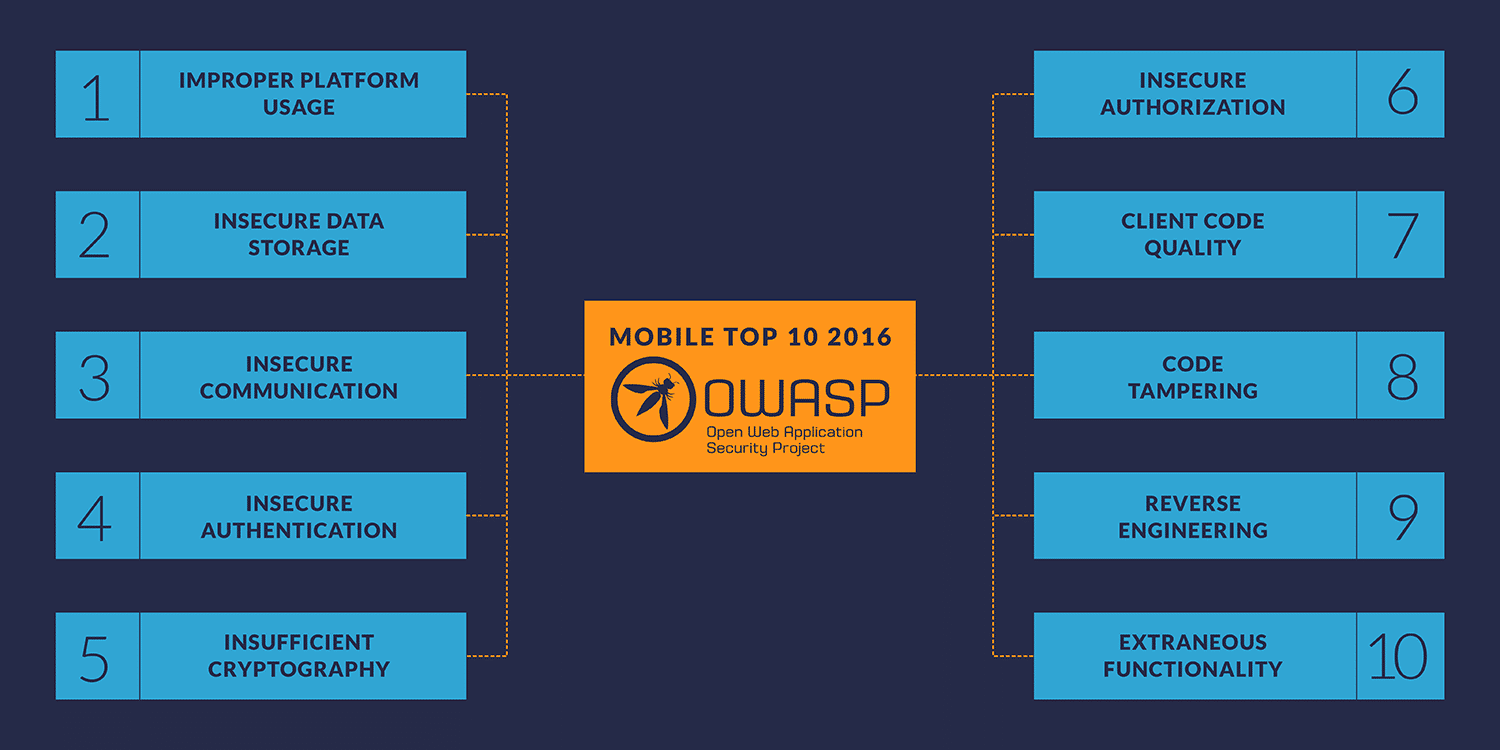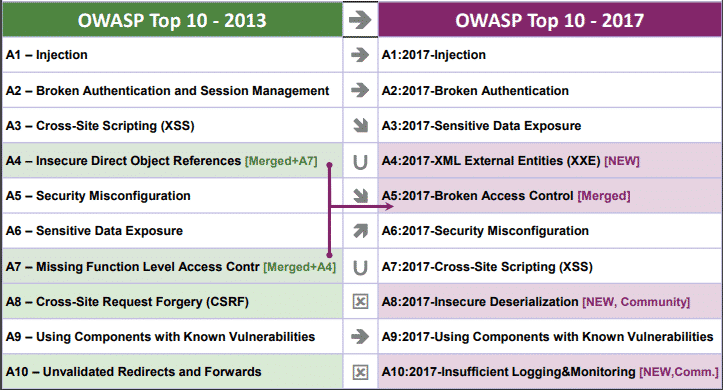
Why OWASP Top 10 (web application) hasn't changed since 2013 but Mobile Top 10 is as recent as 2016? - Information Security Stack Exchange
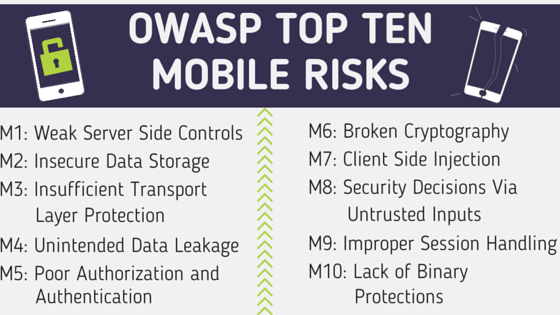
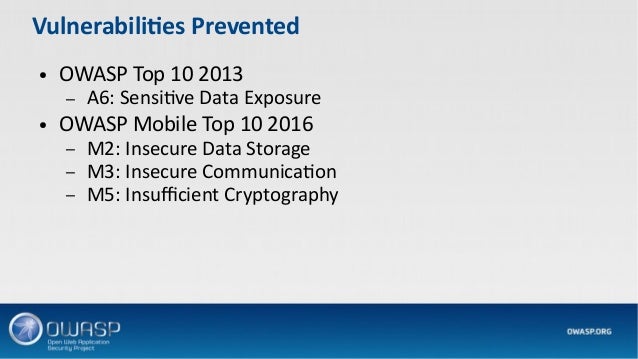
OWASP Mobile Top Ten: Avoiding The Most Common Mobile Vulnerabilities | Checkmarx Application Security